By C. Todd Lopez
WASHINGTON (Sept. 03, 2019) -- During September, the Defense Department and other federal agencies are teaming up to raise employee awareness of indicators that a co-worker may pose an "insider threat" -- of violence or a cyberattack -- during the nation's first Insider Threat Awareness Month.
"Insider threats are posed by persons who use trusted access to do harm to the department's facilities, resources or people," said Dr. Brad Millick, director of the Defense Department's counter-insider threat program within the Office of the Undersecretary of Defense for Intelligence.
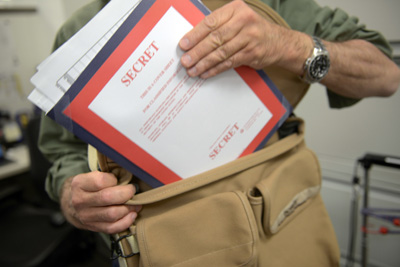
Spies, workplace shooters and disillusioned employees who post sensitive or classified documents on the internet are examples of insiders and their harmful activities. Their actions put lives, missions and dollars at risk.
Millick said an insider may be a DOD employee or contractor or others granted access to DOD facilities, and the threat posed to the department could involve more than stealing classified data. Malevolent insiders could commit workplace violence, sabotage, or unauthorized disclosure of protected information.
Joshua Reese, policy and program advisor for the Defense Department's counter-insider threat program, said DOD has two goals for the inaugural Insider Threat Awareness Month:
-- Educate the DOD workforce about the existence and purpose of the department's insider threat programs. Every Component has one.
-- Encourage the reporting of indicators and potential threats by employees.

Reese said reviews conducted after an insider threat incident -- such as the loss of classified information or an active shooter -- have shown that many of the insider's colleagues were aware something was off, but they never said anything.
"The people of the department, they are the sensors for anything bad that could potentially happen," he said.
And Millick said insiders who plot to do damage often talk about their plans before they act; a phenomenon psychologists call "leakage."
"Workplace vigilance is the key to early detection of potential insider threats," he added. "We want to provide employees with the knowledge to identify warning signs and the ability to report concerning behaviors or indicators."
The Center for Development of Security Excellence, an organization under the Defense Counterintelligence and Security Agency, developed a communications packet to assist Counter-Insider Threat Program managers at each DOD organization in engaging with their respective workforce. The packet includes awareness training, eLearning games, case studies, posters and videos, and all can be found at cdse.edu, including the communications packet itself.