By C. Todd Lopez
WASHINGTON (July 28, 2015) -- "Do you have a map in your car? When was the last time you looked at a compass? Imagine a day when we don't have that technology such as the Global Positioning System, better known as GPS. These are the things we worry about," Capt. James McColl said.
Both McColl and Capt. Justin Lanahan are cyber officers, part of the newly created 17-series Army branch. They both participated in a week-long "hackathon" in Arlington, Virginia, July 20-24, in support of continued development of "Plan X," a four-year, $120-million program at the Defense Advanced Research Projects Agency, or DARPA.
Plan X attempts to, among other things, make it easier for humans to visualize a network and its components, to automate the task of identifying as hostile or benign the anomalies that might appear on that network, to provide intuitive symbology that accurately conveys to users the status of various components of a network, and to make it easier for even inexperienced users to take action to prevent hostile parties from gaining access to and causing damage to a network.
McColl and Lanahan, both Army officers, are participating in the program on a rotational basis. Their participation involves helping develop the program, and also helping to ensure the program will yield results that are useful to the Army.
Any part of a commander's command and control network might include thousands of computers and networking components. The complexity of such networks makes them hard for humans to visualize, and difficult to defend. Plan X is meant to make that task easier.
Adversaries are always looking for ways to exploit networks for their own benefit, McColl said. And that doesn't always mean they use it for their own purpose, or that they want to steal information from it. They might also attack a network simply to disrupt its functionality and deny its use to those who own it.
As part of development of one component of Plan X, DARPA held the week-long hackathon event in Arlington, Virginia. At the event, computer science experts, including McColl and Lanahan, were broken into teams to uncover the best ways to analyze a large set of network data they had been provided for indicators of potentially nefarious network activity. The solutions they would devise to analyze the data, and the code and algorithms they would write to make such analysis easier, would then be used to improve Plan X.
"The overarching idea for the week is 'big data analytics,'" Lanahan said. "The data we have been given is what they call 'net flow.' It contains a minimal subset of all the traffic traversing a network. It tells us what the IP address was, the destination where that packet was going, how big the packet was, and the time that it happened, for instance."
Lanahan, McColl, and about 90 others at the event devised new and innovative ways to analyze for anomalies the "net flow" information they had been given. They hoped to find better, faster ways to identify things that are out of the ordinary, and to be able to accurately differentiate between the anomalies that are due to a misconfiguration of the network, for instance, and the anomalies that are due to malicious activity.
"Maybe you're seeing network traffic at 2 a.m., when no user should be working," Lanahan said. "But when we investigate, we could see that it's a system update, when the Windows updates come out. It could be just that generating traffic. It's an anomaly, but it's not nefarious. Or it could be somebody with a hard drive stealing company data."
Either way, he said, they want to be able to find what is abnormal on the network, identify if it is innocuous or malicious, and then take appropriate action. DARPA's Plan X program aims to make it easier for users to do just that.
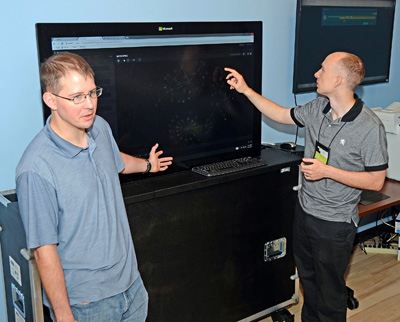
At the hackathon, a physical manifestation of Plan X was on display. It combined both hardware and software. In the flesh, Plan X included a large touch screen monitor - as big as a flat-screen TV - connected to a computer that runs the software. On the screen, the software displayed a wiring diagram of a computer network, though in this case the network was simulated.
Lanathan and McColl demonstrated how one might use the system to monitor and defend a network. Dragging their fingers across the screen, they could zoom in on portions of the network being monitored, and could also touch on individual components to find identifying information about it, or check up on its status.
Lanahan said that a requirement for the system is to have intuitive symbology and indicators that help users quickly see problems as they arise. The symbol that represented one computer might change color if it were infected, for instance. Or it might pulse. Or it might change shape. Another graphic might appear to indicate that a particular part of the network was being hacked, or that somebody was trying to hack it.
"Looking at the screen, you'll be able to have awareness of the network in the same way you might keep track of your unit on Blue Force Tracker," Lanahan said.
The work done at the hackathon is meant to enhance the ability of Plan X to automatically identify threats to the network. During the course of the event, involved teams would periodically insert new code and algorithms into the system to see how they performed, Lanahan said.
When a threat is identified, users of Plan X wouldn't need to be computer scientists or hackers themselves to defeat it. Instead, pre-written software tools that would be part of Plan X would allow users to drag their fingers over a threat to apply a software solution that could block an intrusion or defeat an infection.
With Plan X, it will be easier for operational commanders to understand the network in the same way they might understand the physical world around them, said Ian MacLeod, technical director of Army Cyber Command's Advanced Concepts and Technologies Directorate.
"We need technology to help us translate something we can't touch or feel easily into something we can rationalize about," he said. "To me that's what the Plan X does. It helps us operate in that environment. So the future of this is that these systems, the technology that comes out of this program, will help our forces better understand very complex actions. The domain of cyberspace is larger than any other domain. And with the speed at which it operates, we need computers to help us understand it. When Plan X gets in the hand of operators ... we will bring the military operational mindset to this domain. It helps us to understand the domain a little better."
TWO SEVENTEENS: CYBER BRANCH
Army Secretary John M. McHugh and Army Chief of Staff Gen. Ray Odierno approved the creation of the Cyber branch in September of last year. In October of this year, both enlisted and warrant officers will be included in that branch. But for now, there are only 17-series officers. McColl and Lanahan were among the first to join the branch.
Lanahan said the Army is still defining the work role of a cyber officer, but said the future is promising as the branch continues to grow and evolve by the month.
"At minimum, the cyber mission force is going to be the primary unit we operate in," he said. "We'll be bouncing between the tactical-level cyber mission force, and the strategic-level at the actual service component headquarters or U.S. Cyber Command. So the work roles would look like an operational planning team leader or a mission commander."
McColl said that one role of the cyber officer will be to translate the sometimes arcane language of computers, networking, algorithms and the various types of threats that exist into language that kinetic commanders can understand.
"One of the things we bring is, aside from a love for technology, the ability to translate between military science and computer science," McColl said. "The Army is primarily relying on us to be able to bring cyber effects into the fight. If you think about maneuver elements like infantry and artillery, they are delivering direct or indirect fire effects to a target. For us, we are trying to translate to those kinetic leaders how to use cyber effects to augment their mission. In a situation where dropping a Joint Direct Attack Munition on a building isn't necessarily the best option, we offer an alternative."
Lanahan said that with the new cyber career field, it's important to understand the difference between combat operations, and supporting combat operations. Computers, networks, and radios are often seen as merely supporting a combat mission. But Lanahan said that's not the case anymore.
"Cyber isn't just an enabling mission for the kinetic mission," he said. "Cyber can be an effect unto itself, not just enabling some other kinetic action."
McColl said 17 series officers, and the Cyber branch, are being called on to do more than protect the command and control network so that it can be used by commanders to deliver kinetic effects. Cyber officers must show the commander how if disruption of their own network means they are crippled from doing their mission, disrupting an enemy's network will cripple their ability to do their mission - and that is the digital equivalent to kinetic effect.
"If an enemy was to disrupt our ability to use our GPS, we'd have to go back to map skills," McColl said, though he was quick to point out that infantry and artillery are still adept at using maps. "But we are a more effective, lethal force when those things are protected. And our enemies are less effective and less lethal when they don't have access to the same. If we disrupt their command and control, their logistics, we can cause disarray among their forces. That will better enable our forces to overtake them, while protecting our forces from the same effect."
The Cyber career field will help the Army be able to gain the edge on adversaries, who have become increasingly proficient in the use of technology, McColl said.
Lanahan and McColl, who graduated together in 2011 from the U.S. Military Academy at West Point, New York, said they are excited to be among the first officers involved in the Cyber branch. The newness of the career field, and their early involvement, they say, will provide them an opportunity to chart the future of the career field, and to help the Army develop the best way ahead for cyber missions.
"It's really cool to take something that is emerging, and find a way to best put it for the defense of the nation, either offensively or defensively," McColl said.
"It's hard sometimes in the Army, with its size and complexity, to influence how things are done," Lanahan said. "But knowing this branch is brand new and that there are only 100 of us in the branch now - we can have an impact."
McColl likened his and Lanahan's roles in the Cyber branch to that of the first aviators in the military - back when the Army signed a contract with the Wright Brothers in 1909 for the first military aircraft. Then, as now, those first involved worked daily to find new applications for a technology that continued to advance as quickly as a use for it could be found.
"It's like back when airplanes just came out," he said. "First you're trying to figure out what you can do with an airplane. It can only fly for 15 minutes, maybe. Then later it flies for 30 minutes... and then it flies faster. With cyber, we're on that driving edge of how to make it better and make it do things to improve the way we fight."